‘Not your keys, not your coins’ is an expression often used in the crypto space and for good reason. A private key is a part of a wallet that is used to spend the funds held within it. Therefore, if you don’t hold the private key to the wallet that stores your funds, you are entrusting a third party with your crypto. This is true for most crypto exchange wallets and is a good reason to move your funds to a wallet in which you own the private key to.
There are many different types of crypto wallets and each has their own benefits and drawbacks. It is up to you to choose a wallet which will cater to your specific needs.
Hot and Cold Wallets
Cryptocurrency wallets can be split into two main categories based on the way they operate:
1. Hot wallets
2. Cold wallets
A hot wallet is any wallet that is connected to the internet. If you set up an exchange account you will have a hot wallet created to store your crypto in. These wallets have the advantage of being easy to access and use. However, they are at a greater risk of being hacked or facing other security issues. Therefore they should be treated accordingly and only used to store small amounts of crypto for transactional use. The same way you don’t carry your life savings around in your actual wallet everyday.
A cold wallet is not connected to the internet and uses a physical medium to store the keys offline. This provides much better security and makes them resistant from online hackers. The only way you can have your funds compromised is if someone gains physical possession of the cold wallet and accompanying pins or passwords. Cold wallets are the most secure but are less convenient to use. They are ideal for long term storage and a necessity if you are planning on holding any more than a few hundred dollars in crypto.
Types of Wallets
There are 2 main categories of wallets:
- Hardware wallets (Cold)
- Software wallets (Hot)
Hardware Wallets
A hardware wallet stores private keys in a secure physical, electronic device. These use a random number generator to generate the public and private keys. These keys are then stored in the device itself which isn’t connected to the internet. Many hardware wallets have screens which provide another layer of security as you can add a pin or password to the device. It also allows the device to generate a recovery phrase for secure storage. The recovery phrase can be used to recover the funds should the physical hardware wallet get damaged or lost. Therefore this recovery phrase should be stored as securely as the wallet itself.
The best hardware wallets on the market are Ledger and Trezor wallets.
Software wallets
There are a few different types of software wallets based on how they are accessed. The most common types are:
- Web wallets
- Desktop wallets
- Mobile wallets
Web Wallets
Web wallets can be accessed through your browser without the need to download a program. This makes them easy to use and user-friendly The drawback of this wallet type is that you are entrusting a third party to store and manage your private keys. This means your private keys will be stored on a server, are constantly online and could be susceptible to hacks.
Coinbase and Blockchain.com are two of the largest companies that offer web wallet services.
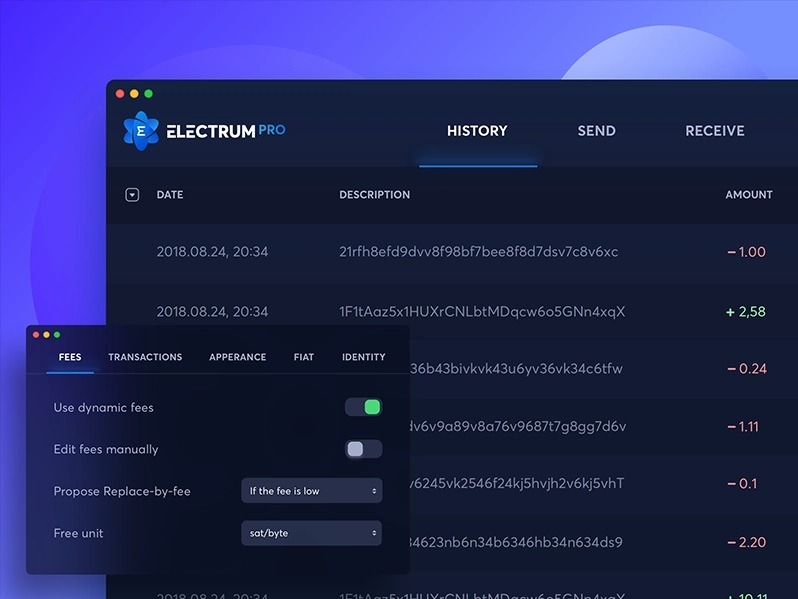
Desktop Wallets
Desktop wallets are software that you download and install on your computer. Unlike the web wallet, a desktop wallet gives you full control over your private keys. Upon generating a new desktop wallet, a file called ‘wallet.dat’ will be created on your computer. This file will store your private keys and if you lose it you will lose access to your funds. Therefore its important to create a backup of this file, store it securely and encrypt it with a password. Desktop wallets are generally more secure than web wallets but it should be noted that they are still connected to the internet which makes them less secure than hardware wallets.
Exodus and Electrum are two of the top rated desktop wallets.
Mobile Wallets
Mobile wallets are available as an app for your smartphone. They offer an easily transportable crypto wallet that can be used for purchases in shops or buying and selling crypto on the go. The drawback of these wallet types are that if your phone is stolen, hacked or infected then you risk losing your funds. It is important to make use of all the security features available when using a mobile wallet such as two-factor authentication. It is not advised to hold large amounts of crypto in a mobile wallet or any hot wallet due to the security risks involved.
If you enjoyed this article, why not sign up for our brand new Crypto Newsletter, with a round-up of the last week’s crypto news, podcasts, and crucial information that you might have missed! Sign up here!